The Equifax Data Breach
16 September 2017
#BrandManagement • #ProductManagement • #ThoughtLeadership • #CustomerExperience • #Security
What did Equifax get wrong during the data breach fiasco? Pretty much everything. Let's break it all down with a laundry list of shocking missteps and bad, bad mojo.
For context, the actual breach event happened in May, but Equifax didn't say anything until 7 September 2017. More than a week later, Equifax still seems guided more by hubris than contrition.
My apologies to David Letterman; this Top Ten list isn't one bit funny. Actually, some of it sounds more like Stupid Human Tricks.
To Equifax CEO Richard Smith: This didn't have to happen. If you and your people were getting the job done — and that job is looking out for your customers — you'd be sitting comfortably on a massive pile of money right now. Instead, it's all going down the drain.
- Back in February, Equifax more than doubled the annual fee I was paying (as a long-time customer) for its 3-in-1 monitoring service, jumping from $64.95 to $149.50
- Equifax IT security "professionals" failed to implement an Apache Struts security patch that was made available in March (Sophos, Wired)
- These same nincompoops (yahoos?!) actually used the password "admin" on a database for Equifax operations in Argentina (BBC)
- Crafted a website to address the breach; at launch, it was a horrible, user-hostile experience (EquifaxSecurity2017)
- Equifax failed to notify customers directly; actually, they refused to notify customers directly, instead — by design — they relied on the media to do the job (Q: "Why am I learning about this incident through the media? Why didn't Equifax notify me directly?" A: "Equifax issued a national press release in order to notify U.S. consumers of this incident and has established a website, www.equifaxsecurity2017.com, where U.S. consumers can receive further information.") (Equifax)
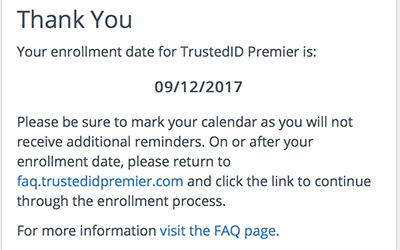
- Required customers to make note of when to return to activate a TrustedID account; no reminders will be sent
- Initially, before customers could even find out if they were impacted by the breach, Equifax required they first give up the right to be part of a class-action lawsuit; this has since been rescinded — but the intentions are clear: it's never been about protecting customers, it's been about protecting Equifax's interests
- A week later, CEO Richard Smith wrote an unimpressive, unconvicing Op-Ed for USA Today
- Top leadership (including Smith) sold shares before the announcement — maybe they didn't know about the breach and they were innocent trades, but it's bad optics and nobody's talking (most likely so they don't say something stupid and make things even worse) (NPR)
- On Sept. 15, Equifax announced the "retirement" of CIO Dave Webb and CSO Susan Mauldin; Equifax continues to protect its own by not even including their names in the press release (Equifax, CNNMoney)
Here's the aftermath, so far:
- Approximately 143 million Americans impacted; it's still not clear how all of this impacts international customers, including Canadians
- 23 class-action lawsuits (and counting)
- At least two congressional hearings
- An FTC investigation (Washington Post)
- A Consumer Financial Protection Bureau investigation
- Equifax stock has plunged 35%, dropping from $142.72/share right before the announcement to $92.98/share on NYSE
- My over-priced account, a contributing factor in Equifax stock's run-up to an all-time high of $146.26/share: CANCELED
In my opinion, Smith should be removed from his position (ultimately, he failed everybody) and Equifax should be run out of business — any and all complicit in this debacle should never be allowed to work in a position related to security ever again. That's my hard line, unapologetic response to this ham-handed display of systemic failures and their associated tone-deaf communications programs.
These pirates took my money as a fee to protect me, then they — almost willfully, based on the flagrant negligence and ridiculous incompetence that's being uncovered — exposed me. With any luck, it's the overpaid IT personnel and senior executives who'll have the most trouble with their data going forward.
"Instant Karma's gonna get you, gonna knock you right on the head," as John Lennon put it.
The reality is, given the magnitude of the lawsuits, it's unlikely Equifax, founded all the way back in 1899, will be able to survive. And it's a cautionary tale for TransUnion, Experian and other credit-related services out there. It's time for them to get serious about security and stop being the pompous, unmoveable beasts they've behaved as for too long.
There's no time like the present for those companies to review:
- Security protocols
- Verify all of the latest system security patches are tested and implemented
- Craft a meaningful, strategic crisis communications plan
- Learn how to talk calmly and expertly about the problem
- Develop a user-friendly "crisis" site and have it at the ready
- Scale up so customers can be addressed directly and with personalization
- Put customers — and their data — at the tippy-top of the priorities list; when all is said and done, Equifax has proved it's not about revenue growth, it's about the data they live (and will ultimately die) by in the success (or failure) of its protection